How we
can assist
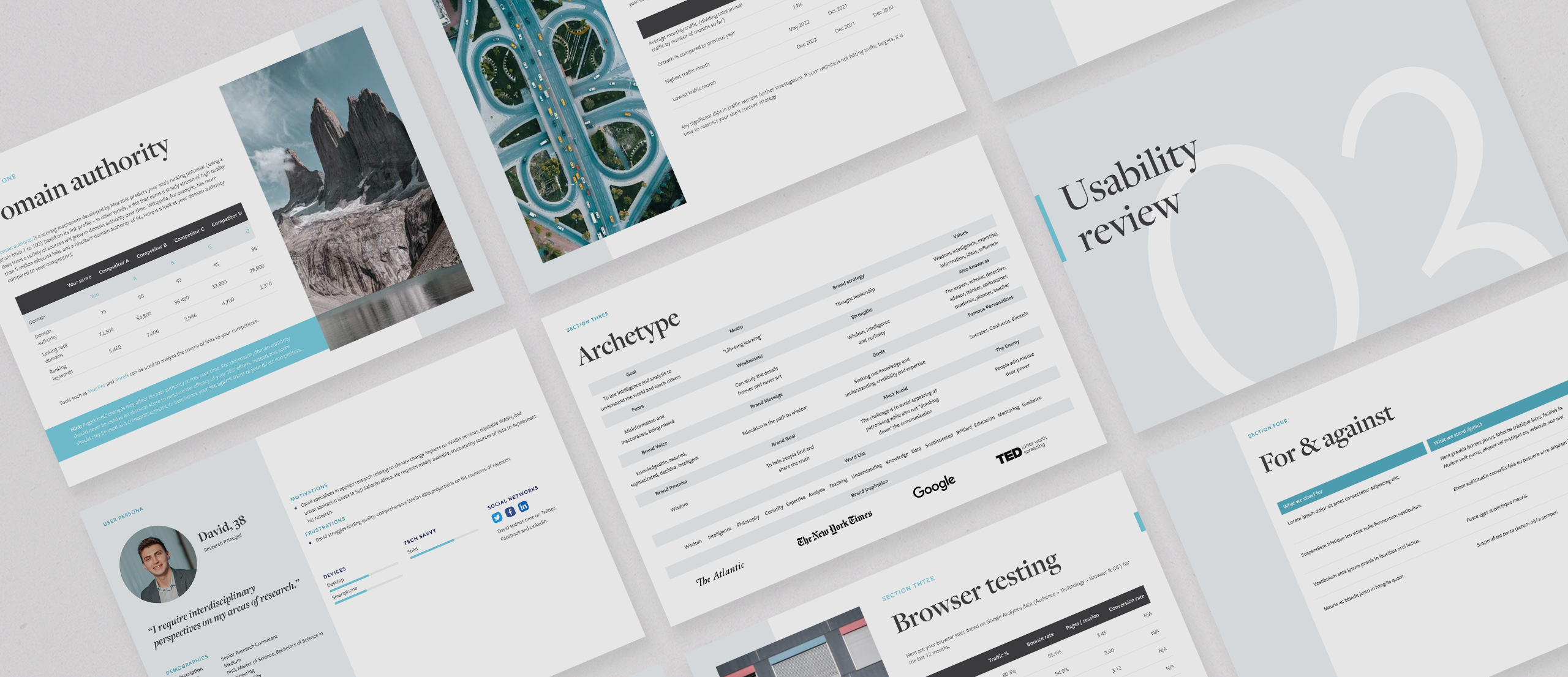
Website
strategy
Web strategy is the North Star of your digital project. It involves synthesizing project requirements with business, brand and audience goals. We work closely with you to unearth opportunities for digital optimization, using a combination of stakeholder interviews, website audits, usability testing and competitor research.
Design
Our design process aims to fuse brand inputs with UX requirements. Design decisions are guided by principles of user empathy, intuitive navigation, clarity of messaging, and alignment with brand positioning.
This is a process refined through continuous user and stakeholder feedback, to create a seamless user experience across your various content channels.

Front end
development
Our front end developers apply extreme precision, attention to detail and multiple rounds of QA when converting web designs into pixel-perfect code. This is a process that prioritizes load speeds, web accessibility and true cross-device and cross-browser support.
Here are just some of the tools and frameworks we leverage during that process:
Backend
development
Our backend developers engineer digital products with the following guiding principles in mind – scalability, security, resilience and ease of content management. We frequently deliver multilingual, geotargeted websites with bespoke content adaptation and security requirements.
Databases are engineered around data governance and efficiency requirements, relying on leading cloud platforms to ensure your content is secure and backed up to multiple environments. Here are just some of the tools we use and love:
Site security
- Many of the websites we develop host access-restricted content and need to be coded to the highest security specifications.
- We follow OWASP guidelines to ensure your site is protected from brute force attacks, SQL injection attacks, cross-site scripting and other potential vulnerabilities.
- Depending on your project needs, we can use insights from third-party penetration testing (also known as “ethical hacking”) to keep your site up-to-date with the latest security protocols.



















